Hello Friends it's time to install the Internet Download manager Fully cracked no any patch
just install and use.
Step 1. for installing you have to download the IDM zip given below icon of download
Step 2. also download any zip extractor you can download win rar from below.
 |
| IDM |
 |
| WIn rar |
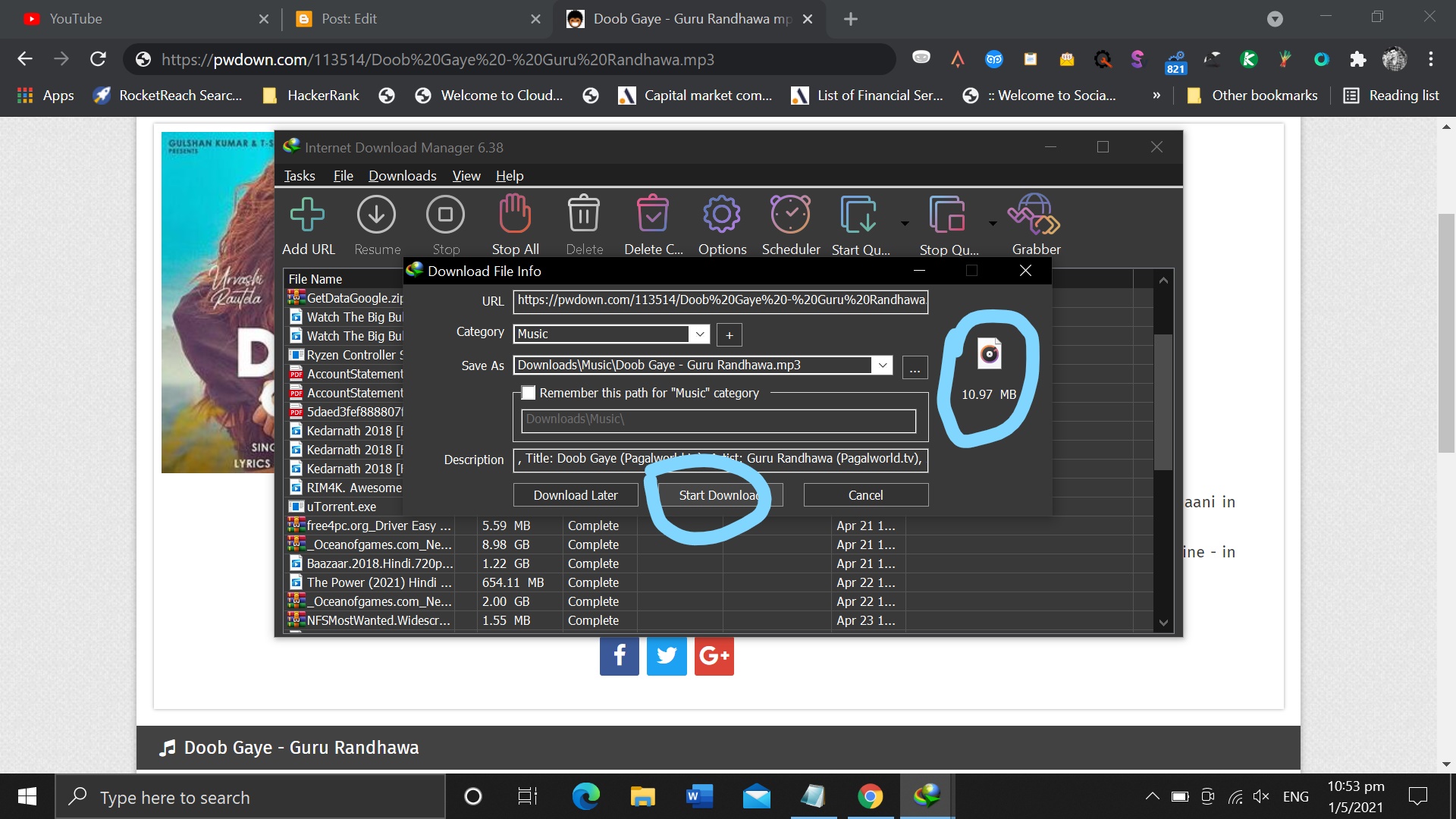
How to use IDM many people confused let's see it's very easy to use :
Step 1. copy the download link of a file.
Step 2. paste to idem top left side option add URL
Step 3. Now you get the option to download the file click ok
See the file has been downloaded
let's play and enjoy
Thanks for visiting my blog
if you want more fun and technical knowledge then get the update by join we


















Idm Cracked Version
ReplyDelete-
Scifi Curoisity >>>>> Download Now
>>>>> Download Full
Idm Cracked Version
-
Scifi Curoisity >>>>> Download LINK
>>>>> Download Now
Idm Cracked Version
-
Scifi Curoisity >>>>> Download Full
>>>>> Download LINK